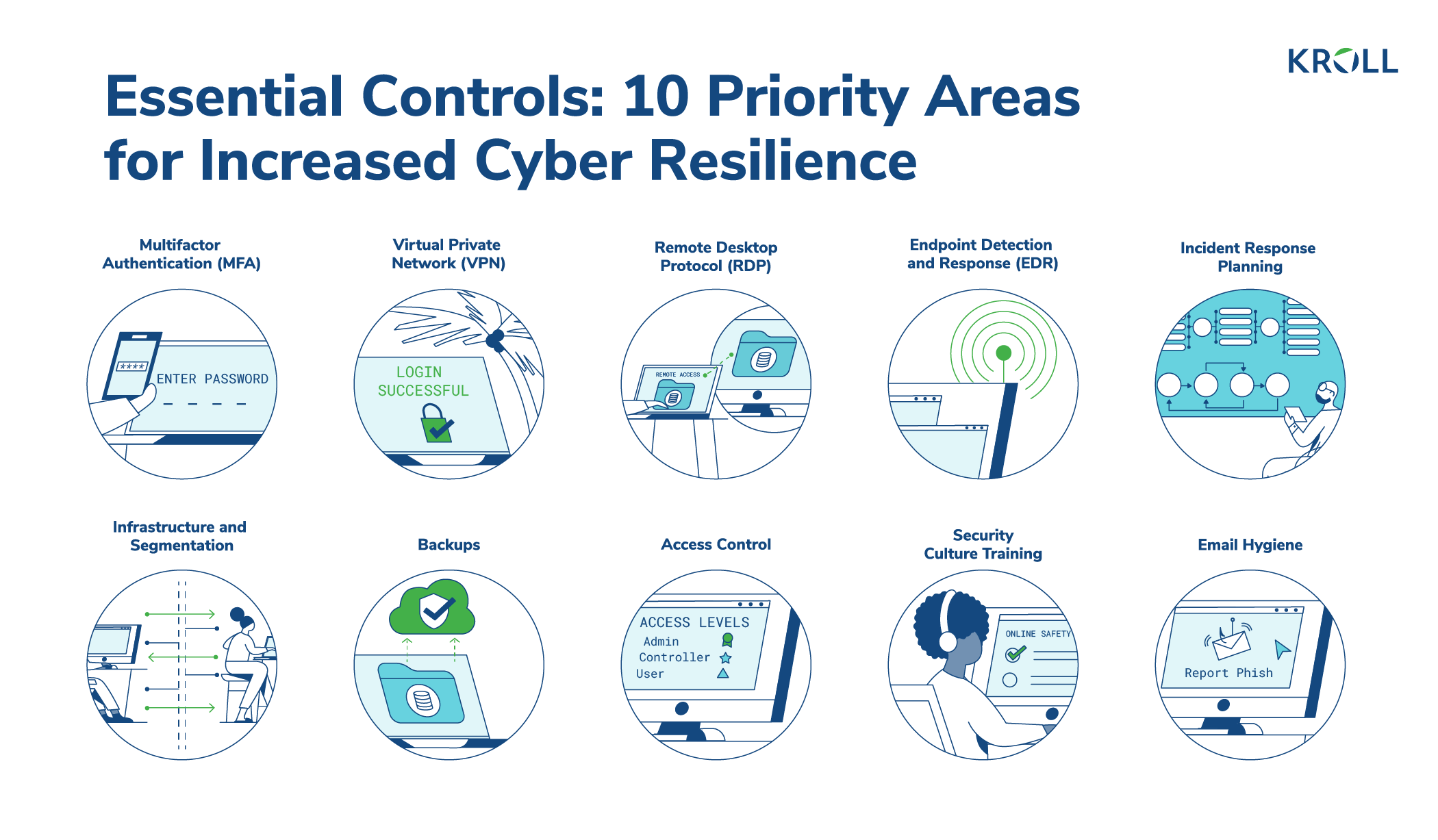
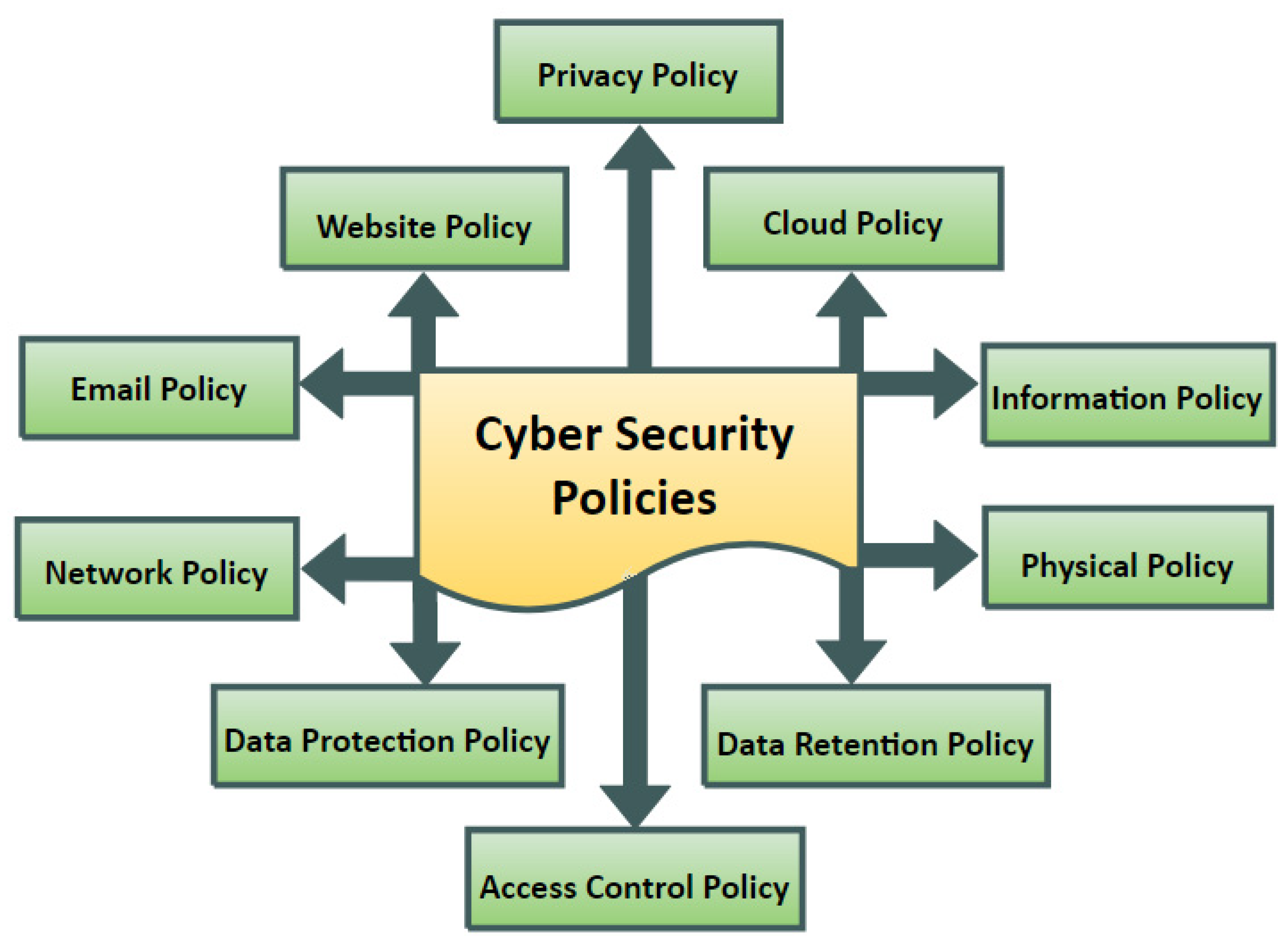
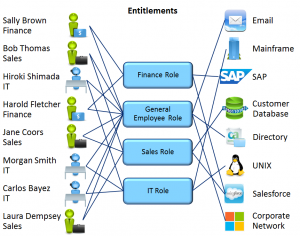
An example of interdependencies between access control and other topics... | Download Scientific Diagram
Access Control Methods Information Security Ppt Powerpoint Presentation Pictures Visual Aids Cpb | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

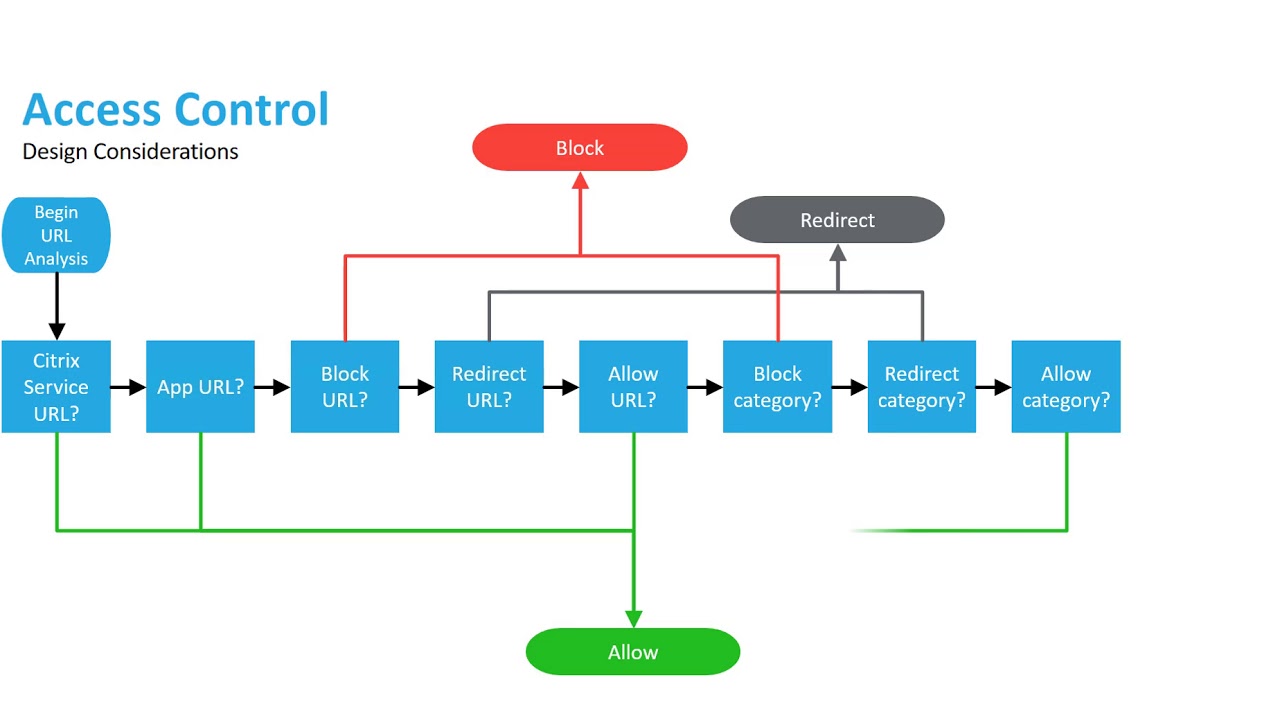
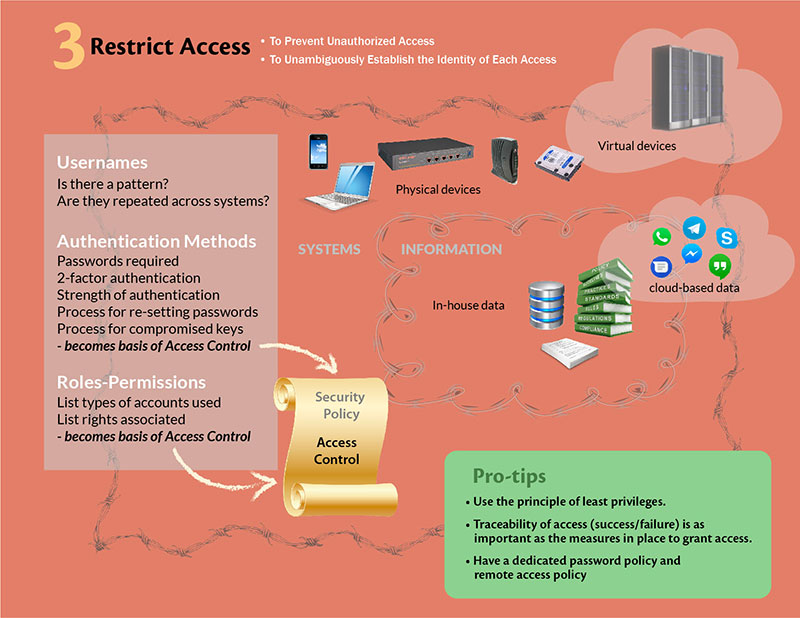
Access Control | User access control | Access Control system |Network access control | Infosec - YouTube

Access Control: Don't Give Cybercriminals the Keys to your Business | 2020-03-05 | Security Magazine

A systematic review on security in Process-Aware Information Systems – Constitution, challenges, and future directions - ScienceDirect